Cybersecurity in the Blockchain
Technological context

The support offered by Apside
-
![startae-team-7txa8xwe4w4-unsplash.jpg]()
1. Training and Onboarding
Raising awareness of the fundamental challenges Understanding the key concepts in order to innovate and drive Mastering the technical aspects in order to develop and integrate solutions
-
![patrick-perkins-etrpjvb0km0-unsplash.jpg]()
2. Innovation and Strategy
Studying the market and analysing opportunities Assessing feasibility and demonstrating value Adopting a strategic focus Drawing up an action plan
-
![brands-people-ax8ia8gajvg-unsplash.jpg]()
3. Governance, Risks and Compliance
Defining operational and technical governance Assessing application performances and security Assessing regulatory compliance
-
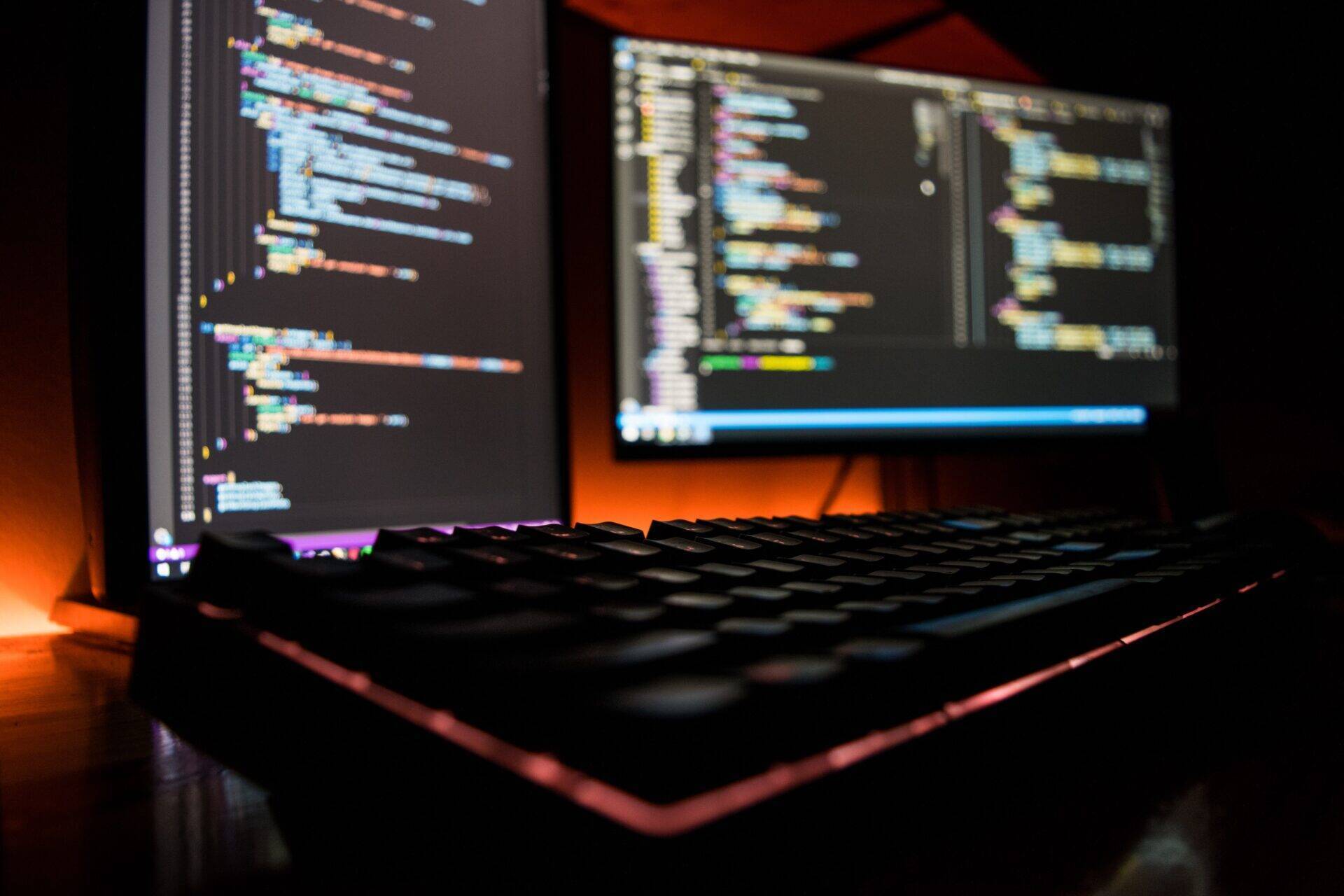
![fotis-fotopoulos-duhkov44prg-unsplash.jpg]()
4. Development
DevSecOps approach Smart Contrats and Dapps Tokenisation platforms, APIs and Oracles
-
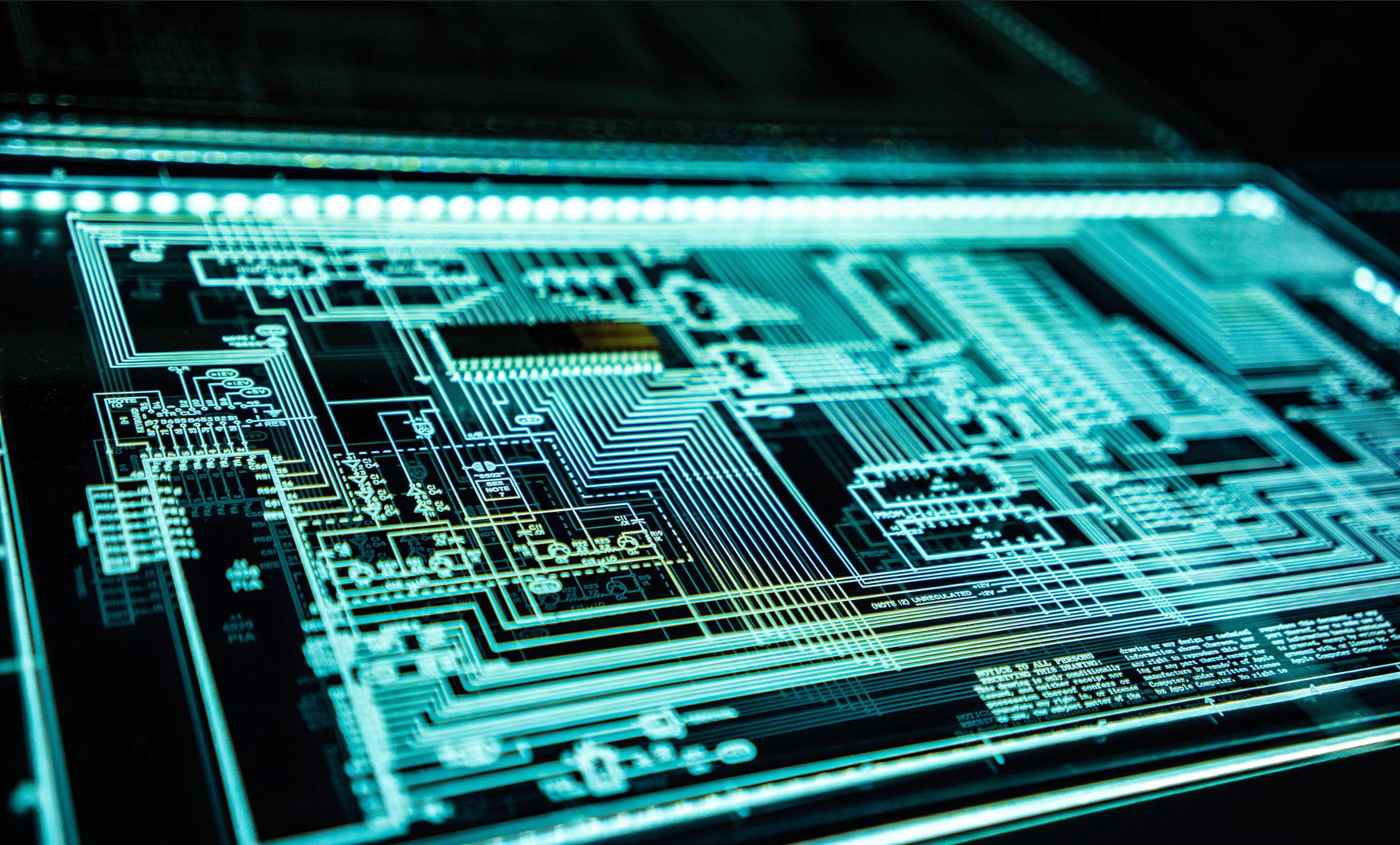
![cyber-min.png.png]()
5. Cybersecurity
Intervening across all software and hardware stacks Conducting security audits and securing the entire system Implementing means of supervision, prevention, detection, and remediation